
The Iran Conflict Is Raising the Stakes for Defense Compliance, Fast
As defense production accelerates, contractors need more than visitor management. They need screening, audit trails, and proof that urgent operations stayed controlled.
New Blog Post · 6-minute read

The new directive shifts the burden from paperwork to operational resilience. If your organization relies on "good faith" IT security, the rules of the game just changed.
The March 2026 White House Cyber Strategy fundamentally reframes national cybersecurity. It isn't just a recommendation—it's a new baseline for how defense contractors, universities, and private schools must operate.
For years, organizations could get by with checklists and architecture diagrams. Now, procurement teams and regulators are looking for proof of resilience. They don't just want to know you have backups; they want to see the recovery drill logs.
"We must detect, confront, and defeat cyber adversaries before they breach our networks and systems... [and] we must be able to recover quickly."— President's Cyber Strategy for America, 2026
Operational resilience is now more important than compliance checkboxes.
Least privilege must be enforced in real workflows, not just in policy.
Your vendors' vulnerabilities are now officially treated as your vulnerabilities.
Cloud security is judged by hard proof of recovery, not just architecture diagrams.
AI is encouraged, but it requires strict human oversight and clear data boundaries.
Planning for post-quantum computing threats is a requirement starting today.
Procurement is going to get much harder. Here is what you need to ask your vendors.
Screenshots, audit exports, and role maps matter more than polished security pages. If a vendor says "we are secure," ask them to prove how their system fails closed under pressure.
Buyers will start asking exactly where privileged logic runs, how failures are handled, and what recovery evidence you can show on demand.
Whether you use SecurePoint Visitor Management or ATLAS integrations, reliability during an incident is now a core part of the product.
At SecurePoint, we don't play "cosplay security." We enforce tenant isolation at the database level, not just in UI roles. Our privileged actions stay secure on the server, and sensitive failure paths automatically fail closed.
We also ensure that no raw personally identifiable information (PII) ends up in telemetry when a UUID will suffice. Defense and education buyers need systems that hold up when an auditor walks through the door, not just when everything is calm.
Or get it sent to your inbox
Weekly insights on sanctions, export controls, and visitor compliance.
Get weekly insights on sanctions, export controls, and visitor compliance delivered to your inbox.
No spam. Unsubscribe anytime.
Related posts
More guidance on sanctions, export controls, and visitor management for regulated facilities.

As defense production accelerates, contractors need more than visitor management. They need screening, audit trails, and proof that urgent operations stayed controlled.
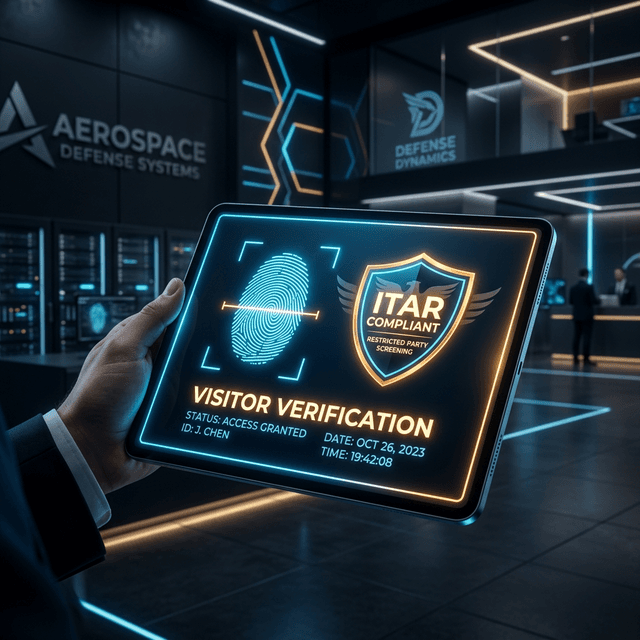
A practical, regulation-grounded guide to ITAR visitor requirements, EAR overlap, screening controls, and audit-ready evidence for defense contractors.

How compliance perception is shifting in 2026 from reactive to proactive and strategic, serving as a growth driver for defense contractors.